Home > Money > News > £5,000 stolen from food writer in simjacking case
£5,000 stolen from food writer in simjacking case
Jack Monroe's phone number was hijacked and scammers subsequently gained access to her bank accounts.
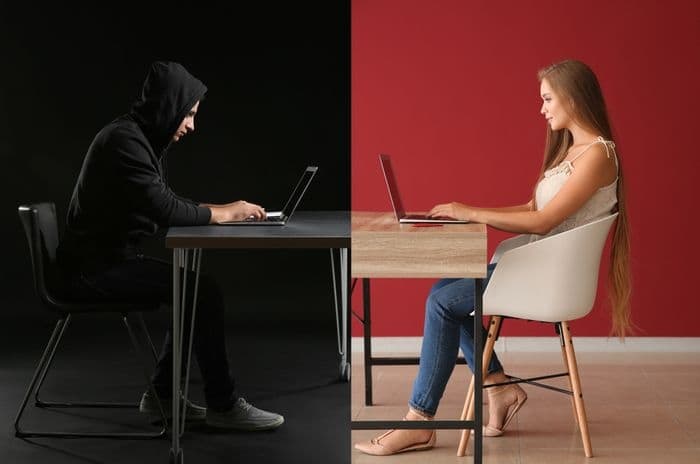
Information either in the public domain or illegally obtained can be used to port a phone number to another SIM via a mobile provider.
The case highlights the risks posed by simjacking or SIM swapping when phone numbers are linked to bank accounts and other platforms.
It raises concerns about the payment industry's reliance on mobile authentication along with data protection methods used by mobile networks.
What happened to Jack Monroe?
Monroe, a food writer known for low-cost recipes, is a high-profile victim of a scam that's becoming more common.
A third party was able to pose as her to her mobile network and inform them that she wanted to port her number to a new network using a PAC code.
While details of how security was bypassed haven't been confirmed, it's likely the scammer will have used information already in the public domain including Monroe's date of birth.
Once the number had been ported, the scammer would have been able to receive any two-factor authentication messages sent by her bank to confirm payments and changes to her bank account.
Monroe estimates she has lost around £5,000 to the scam and doesn't yet know whether she'll be able to recover the money as the payments were technically authenticated by the text messages the scammer received.
It is yet another type of fraud that could fall under the banner of Authorised Push Payment (APP) fraud, where customers are tricked into transferring money or giving personal details to a scammer.
In the case of phone number hijacking, however, it feels as though the mobile network is being scammed and the customer is paying the price.
Flaws exposed
This high-profile case of phone number hijacking exposes some of the flaws in a world dominated by digital financial transactions.
By posing as Monroe, the scammer was able to persuade her mobile network that they were her, answering the security questions associated with obtaining a PAC code successfully.
While it might be easy to say that high-profile people like Monroe are easier to impersonate due to more information about their lives being readily available, it's important to remember that many of us have open Facebook profiles with our date of birth and other personal information on there.
In 2017, it was claimed that social media usage was exacerbating ID theft, with users volunteering more personal information than previously and giving scammers more opportunities to impersonate them.
This followed warnings back in 2015 by fraud prevention organisation Cifas that a third of people weren't taking basic precautions to protect their identities online.
So, in cases of simjacking, it could be suggested that customers haven't taken enough precautions to keep their personal information private and this has helped scammers bypass the security questions of a mobile network. This could hinder chances of recouping the money.
That said, mobile networks may need to improve their security processes to reduce the opportunities scammers have to pose as customers.
Two-factor authentication
Two-factor authentication is also brought under the microscope when cases of phone number hijacking are discussed.
Put simply, two-factor authentication allows a single use code to be sent to a mobile number associated with an account. That code is then entered to verify the payment.
The rationale behind two-factor authentication is that a customer will have their mobile with them, so verifying via this method is a secure way of ensuring they're the ones accessing their account or making a payment.
Phone number hijacking subverts this process, with scammers able to access those two-factor authentication codes before the customers even knows their mobile number has been compromised.
It isn't just banks that use two-factor authentication, with large online companies bringing in security measures that require customers to use the mobile number associated with their account to verify their purchases.
Unless action is taken by mobile networks and banks to reduce instances of SIM swapping, it's feared many more people could fall victim to this type of fraud.
Receive consumer updates that matter in our newsletter

We're independent of the products and services we compare.

We order our comparison tables by price or features - never by referral revenue.

We donate at least 5% of net profits to charity, and operate a climate-positive workforce.


