By changing passwords and altering some settings on our wireless router, we can immediately improve our router's security.
Plus, understanding how hackers use lax security settings to gain access can encourage us to take some time and tighten security.
With some high-profile router hacks in the not-too-distant past, wireless router security is as crucial as ever.
Why protect wi-fi routers
Our home router is the gateway to our entire home network, so protecting it as much as we can will ensure we're protecting our laptops, mobiles, tablets and smart home devices.
Occasionally, we hear about high profile router security issues such as Sky's major security flaw in 2021, which enabled hackers to easily take out a home network.
Another example came in 2018 when a security flaw was found in Hyperoptic's home routers due to all routers having the same hardcoded root password.
Virgin Media's Super Hub 2 was also found to offer poor protection in 2017, with the default password 'crackable' within just a couple of days.
So, even when we're provided with a router from our broadband provider, it's still vitally important to take steps to ensure our home router is as secure as possible. We've assembled seven steps to get us there.
1. Password protect the router
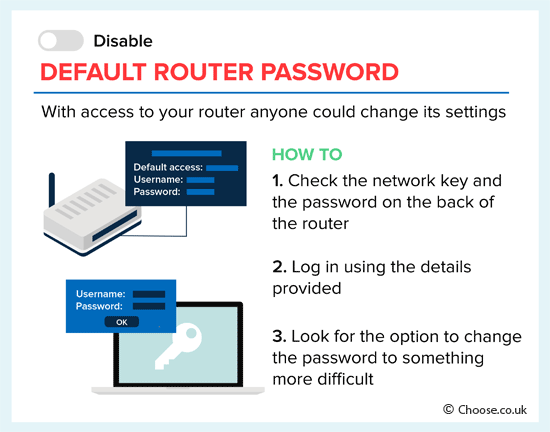
Changing the pre-set passwords on a router is the first step to ensure router security in the home.
This password isn't the one we use to log on to the wireless network in our home. Instead, it's the generic password for the router that can easily be found online if someone wants to look and then use that information to compromise your router.
Once someone has access to our router, they can theoretically lock us out of our wireless network by changing other settings include the network key (our wi-fi password), so don't skip this step.
To change the router password, check for a sticker or panel on the back of the router that includes the network key: some ISPs include the router or admin address (http://192.168.x.x or similar) and the password on this label.
Navigate to this address in a computer browser and log in using the details provided, then look for the option to change the password to something more difficult and unique - and keep a note of the new password somewhere safe.
The password set here should be strong and shouldn't include any personal details that are easy to guess such as street or pet names. If there is one password you make as complicated as possible, make it this one.
It's also worth looking to see if there's an option to restrict admin access to the router to connections made via an Ethernet cable - so that once secured, only those with physical access to the router can change these settings.
Once the router password has been changed, stay logged into the screen to carry out the next few security checks.
2. Password protect the network
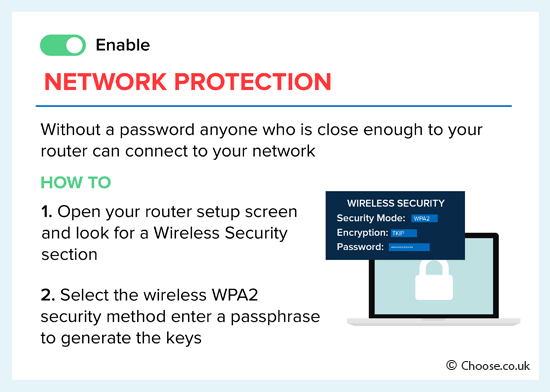
The next step is to change the password we use to log in to the network on our devices. This is called the network key, although it's more commonly called a wi-fi password.
This password can also be changed within the account security screen mentioned above, so find the correct field and alter the password to something unique and tricky to guess. As we discuss in our guide to avoiding email scams, passwords are the strongest line of defence we have against hackers and scammers.
You can try to change this password occasionally, to improve the security of your network, although because this can be time consuming to then update on any connecting device, ensuring you use different passwords is a better tactic. This is because if any online shopping logins are ever leaked, it reduces your security risk as you'd ideally not be using the same password for anything else.
We can use a reputable password manager like LastPass or 1Password to help create strong passwords that we don't have to remember individually - the software remembers it for us. The only thing to remember then is the password for the software. That must be written down somewhere safe (offline) or we may lose access to all our accounts.
Learn more about password security in our guide to staying safe while browsing and shopping online.
At the same time as changing our network key, we should also select the right level of encryption for our network.
There should be a "security" tab or menu, showing the various options for encryption - do not choose "none". At minimum, we're looking for WPA2, while newer routers will have an option for WPA3.
Encryption
Internet security protocols have evolved over the years, but the latest standard we should be aware of is WPA3. This was introduced in 2018 and is gradually being implemented in suitable hardware.
While many newer router models from major broadband companies in the UK now offer support for WPA3, many are still being supplied that only support up to WPA2.
WPA2 stands for Wireless Protected Access 2 (WPA2). As we'd expect, there was a WPA used before this, and that in turn replaced Wired Equivalent Privacy (WEP).
What we need to know about WPA2 is that it uses Advanced Encryption Standard (AES) to secure networks instead of Temporal Key Integrity Protocol (TKIP).
That's why, if there's a choice, we should always choose WPA2 [AES] over WPA2 [TKIP].
One of the strengths of WPA2 encryption is that it gets us to set our own password - which we should make as difficult as we can, thus helping to ensure that only the people we tell the password can log on to our home network.
If WPA3 is an option, that should be selected as it offers even more secure encryption than WPA2. WPA3 addresses vulnerabilities found in WPA2, it also uses 192-bit encryption compared to WPA2's 128-bit AES.
Devices released prior to 2018-2019 are unlikely to support WPA3 though, so most routers will allow a mixture of WPA3 and WPA2 connections as a fall-back for older devices.
3. Change the SSID
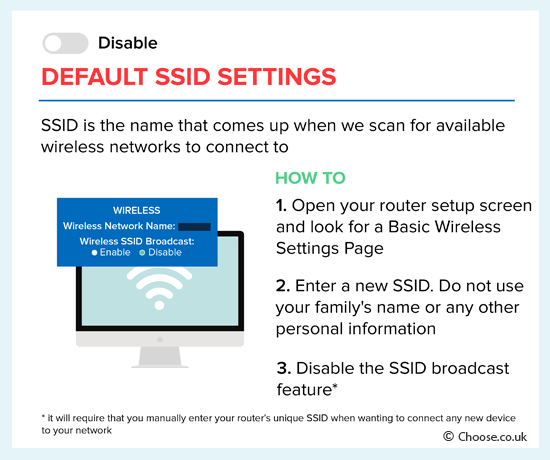
Modifying or hiding the SSID (Service Set Identifier) is the next step on the way to home router security.
The SSID is the name that comes up when we scan for available wireless networks to connect to, and most include more or less detail about the ISP and router model broadcasting the signal - run a scan and note how many start with "TALKTALK", "Sky" or "BTHub".
That gives hackers and other unwanted guests a place to start when checking if we're using default passwords as we cautioned against in Step 1.
To change the SSID, go to your "router setup" page and look for the "wireless settings" option. Here you should be able to enter a new SSID. Be sure to use something less revealing and steer away from including any personal information or your address.
Given how many devices most of us have connected to our home wireless network, it's often not practical to hide the SSID - but doing so means the neighbours and any casual chancers won't see it on their list of networks when they're looking for a connection.
4. Switch off WPS
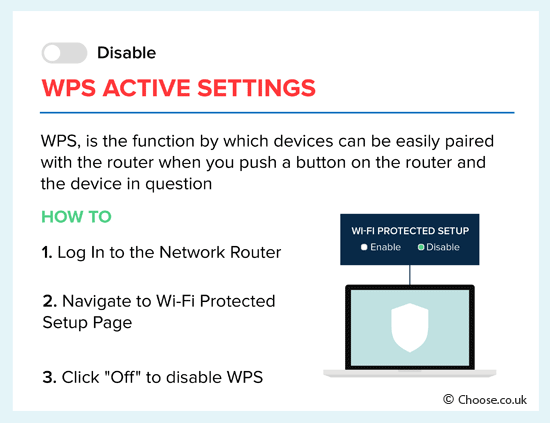
Deactivating WPS may seem counter-intuitive considering how many ISPs boast their router has WPS functionality, but it could be dangerous to leave it switched on.
Wi-fi Protected Setup, or WPS, is really useful for connecting new devices to a wireless network quickly and easily - simply select the WPS option on the device, then push a button on the router and access is granted.
It works by synchronising with - and granting access to - any devices in the surrounding area that are primed to receive WPS data.
While the obvious risk would seem to be from people hanging around our router to try to take advantage of these mini broadcasts, WPS can also be cracked fairly swiftly by hackers once they know just a few basic details about the router setup.
Once they've cracked the WPS, they can go on to access our other security details much more easily - so if in doubt, switch it off.
To disable, log into your network router and go to the wi-fi protected setup page then simply click the "off" option.
5. Disable remote administration
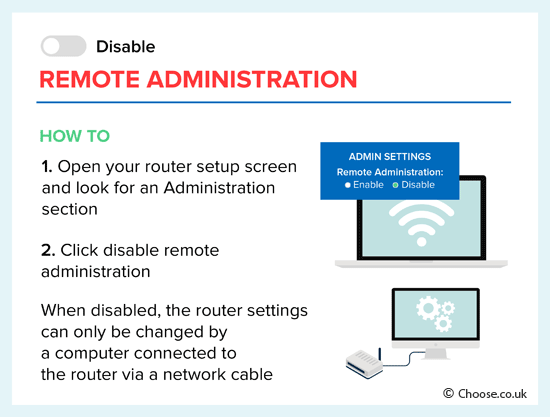
Deactivating remote administration ensures only connected devices can access the administrative interface.
If this feature is switched on, hackers can penetrate a home internet connection via the remote administration feature on a router, which exposes its web interface.
Luckily, remote administration can easily be disabled via the "administration" tab on the router's setup screen.
Those who require remote access should consider using an alternative method such as a VPN, which offers more protection.
6. Enable a firewall
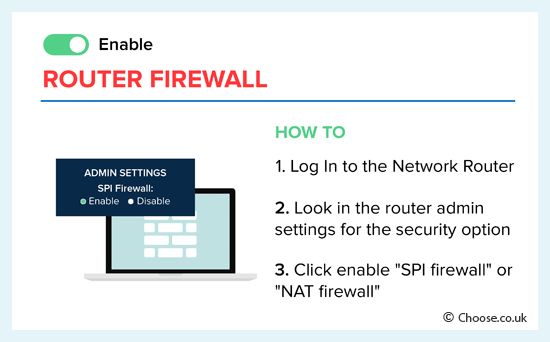
Switching on a router firewall will help stop unauthorised traffic attempting to connect to our computer via the internet.
Almost all routers have a built-in hardware firewall which is a far more robust defence than any software firewall.
The instructions to activate the firewall will be in the router manual, or on the ISP's router help pages - but it may be as simple as looking in the router admin settings (from Step 1 ) for the security option that says something like "SPI firewall" or "NAT firewall", clicking enable, and then saving and applying that change.
Remember, however, that a firewall on its own doesn't protect against viruses so always have anti-virus software installed and up to date.
We've got more detail on staying safe online in our guide to parental control software.
7. Setup a wireless MAC filter
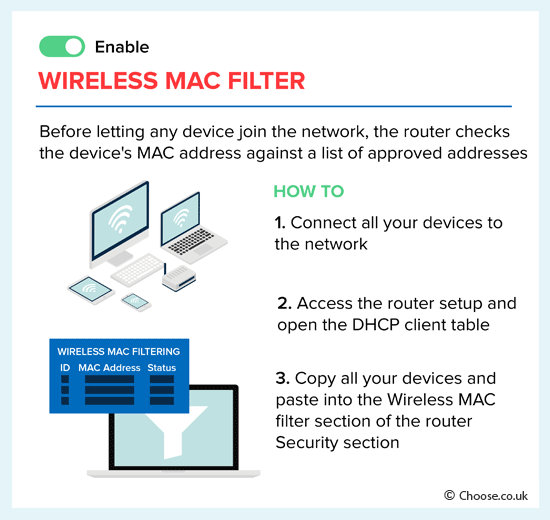
Filtering MAC addresses can limit the devices able to connect to a network.
Most routers offer this option, sometimes known as hardware address filtering, in a bid to keep hackers at bay and boost overall security.
When enabled, the router will check the MAC address of any device requesting to join a network against a list of approved addresses. If the address corresponds with one on the list then access is granted - if not, it's blocked.
To put a wireless MAC filter in place, go to the router set-up page and open up the DHCP table. Here we have to enter the MAC address of each device we want to give access to. We'll also need to provide a description for the item and make sure the status says "enabled" then save our changes to implement them.
We can find the MAC addresses of our devices within their wi-fi settings. If in doubt, do a quick search on where to find the MAC address for a particular model.
Extra router security tips
Implementing all the security tips we've discussed in this guide will help protect a home's router, but here are a few bonus ones too.
- Be sure to update a router's firmware if it needs to do an update. These will usually be downloaded and installed automatically (check the router security page within your ISP account) but get into the habit of checking if an update is available.
- Disable the router if you're away from home. If practical (i.e., there are no devices that need the internet while you're away), turning off the router when you're away for a long period will prevent security problems occurring when you're not around to deal with them.
- Increase protection on other devices. It's one thing to have a secure router, but make sure that's matched by smartphone security and other device security too.
- Use guest network options if you need to. Some routers allow households or businesses to broadcast a so-called guest network which grants wi-fi access without letting a guest into the main network.
Remember, too, that laptops, tablets and mobile phones are rarely the only devices we have to think about security for these days.
In 2024, the UK became the first country to introduce a law to safeguard consumers against hacking while using internet-connected smart devices, initially proposed in 2020. Under new laws, manufacturers must adhere to basic security standards, such as not using easily guessable default passwords, and prompting users to change the password upon start-up.
99% of UK adults own at least one smart device, with the average household owning at least nine. These devices can include baby monitors, smart speakers, televisions, and even washing machines and dryers, so security can easily be overlooked.
Summary: Keep routers secure
The steps outlined in this guide will go some way to protecting a router from external threats, whether these come via the internet or from a malicious neighbour trying to break into our network.
Most of them can be set up when you get a router and only need to be considered periodically, so it isn't as much work as it may seem on an ongoing basis.
Keeping network security in mind at home should start with the router and incorporate anti-virus software and device security. It's also important to protect personal details when online to ensure no one can scam you in other ways - read more about that in this guide.
Finally, remember that router security is constantly evolving. As routers and more connecting devices catch up to the new WPA3 encryption there will be even more security protocols protecting us.









